SIEM – Open Source Solutions
What is SIEM and what’s its benefits ?
SIEM (Security Information and Event Management) is a hybrid of Security Information Management (SIM) and Security Event Management (SEM). A SIEM system analyzes security warnings issued by apps and networks in real time. SIM is the gathering, monitoring, and analysis of security-related data, such as log files, into a centralized repository for trend analysis.
SEM is a network event management procedure that includes real-time threat analysis, visualization, and incident response. It works by centralizing the storage and analysis of logs or events created by other software operating on a network using data inspection tools. SIEM solutions are useful for detecting cyber assaults and providing real-time analysis of security warnings.
SIEM products that are free and open source have lately gained favor. While their capabilities are restricted (in comparison to their paid equivalents), they are widely used in small to medium-sized businesses. In this article will take a look at some of the greatest free and Open Source SIEM technologies available today.
Open Source SIEM technologies :
1- AlienVault OSSIM
AlienVault created OSSIM as a unified platform with some of the most valuable security capabilities, such as:
- Asset identification
- Detection of intrusions
- Correlation of SIEM Events
- Evaluation of Vulnerabilities
- Monitoring of behavior
OSSIM performs event collection, normalization, and correlation, making it a comprehensive solution for threat detection. It provides features for short-term logging and monitoring, long-term threat assessment, and built-in automatic responses. Some of the tool’s advantages and disadvantages are as follows:
Pros:
- Can be used both on-premises and online.
- Only one server is required.
- There is community support available through its product forum.
- Developers provide continual development, which increases the value to users.
Cons:
- Due to its limited versatility, customisation is a time-consuming procedure.
- Setup is time-consuming.
2- SIEM Monster
SIEM Monster combines many Open Source solutions into a consolidated platform and delivers real-time threat information, safeguarding its customers from real-time threats.
SIEM Monster has the following features:
- Human-Based Behavior- It includes correlation options to ensure that the threats recorded are accurate and that false positives are kept to a minimum.
- Threat Information- Stopping real-time assaults with commercial or open source threat intelligence.
- Deep Learning- Machine Learning is at the heart of this function, teaching the software to automatically destroy any potential threats.
- One significant advantage of this technology is that it may be used on-premises or in the cloud.
3- Wazuh
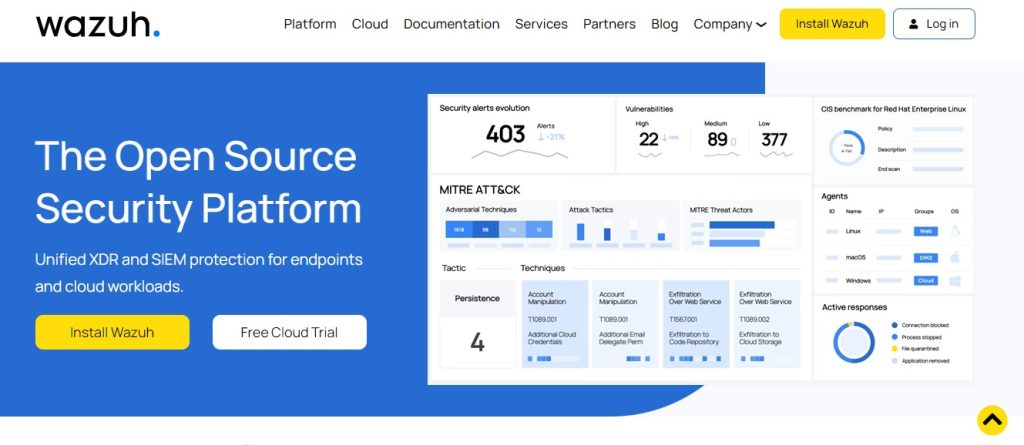
Wazuh gathers, aggregates, indexes, and analyzes security data, allowing enterprises to detect intrusions, identify risks, and discover any behavioral irregularities. It has several advantages, including:
- Detection of Intruders
- Analysis of Log Data
- Monitoring of File Integrity
- Vulnerability detection, configuration assessment, incident response, and regulatory compliance are all part of the process.
- Cloud safety
- Container safety
Wazuh is an excellent corporate solution since it is flexible, scalable, free of vendor lock-in, and has no licensing fees. Its disadvantage has been a constraint in its ability to manage many notifications, which somewhat jeopardizes its integrity.
4- Snort

Snort is a free and open source intrusion detection system (IPS). It is an excellent solution for businesses looking for a platform that can perform real-time network traffic analysis.
It also has log analysis features and the ability to show traffic or dump packet streams to log files. A user manual, FAQ file, and tips on how to find and utilize Oinkcode are available to users. Snort has three excellent applications:
- As a packet sniffer, such as tcpdump
- As a packet logger, it is particularly useful for troubleshooting network traffic.
- Snort, being a complete network intrusion prevention system, is quite technical in nature, with an unfriendly user interface.
5- OSSEC

Is a host-based, scalable, multi-platform, open source intrusion detection system. It is widely used because it is compatible with most operating systems, including Linux, OpenBSD, FreeBSD, MacOS, Solaris, and Windows.
OSSEC boasts a sophisticated correlation and analysis engine that includes elements such as;
- Analysis of logs
- Monitoring the integrity of files
- Monitoring the Windows registry
- Policy enforcement is centralized.
- Detection of rootkits
- Alerting in real time and active reaction
- Inventory of Compliance Auditing Systems
6- logit.io
Logit.io offers a low-cost SIEM solution based on hosted ELK. ElasticSearch, Logstash, Kibana, and Beats are among the SIEM products that make up the ELK Stack. ELK is also a fundamental component in the architectures of OSSEC, Apache Metron, SIEM Monster, and Wazuh, all of which are described in this blog.
Among the features are:
- Advanced access controls based on roles
- Deployment in record time
- Hundreds of integrations are available.
- Auditing and compliance
- Low-cost SIEM Event Correlation
- Reports that are scheduled
- Notifications and alerts
7- Splunk Free
Splunk Free, as the name implies, is the free version of Splunk Enterprise. Splunk Enterprise is a robust SIEM solution, and its free version shares many of its capabilities, but it may not meet all of your organization’s security demands, especially as it expands.
Splunk Free lets you index up to 500MB of data each day and gives you lifelong access (no expiration date).
Some functions of Splunk Free are disabled, including:
- Alerting/monitoring
- Because there are no user roles, there are no login capabilities.
- Capabilities for deployment management
- Clustering of indices
8- Mozdef
Mozdef was created by Mozilla and is hosted on Amazon Web Services. It’s one among several tools accessible to attackers to help them organize, exchange intelligence, and fine-tune operations in real-time.
Mozdef’s development goals include the following:
- Providing a platform for defenders to find and respond to security problems in real-time.
- Providing the metrics required for security events and incidents.
- Facilitating repeatable, predictable incident-handling methods.
- Improving real-time cooperation in incident response.
9- Security Onion Solution
Security Onion is a Linux distribution that specializes on intrusion detection and enterprise security monitoring (ESM). Doug Burks created it in 2008 and then established Security Onion Solutions in 2014.
Security Union is a collection of security tools such as Elasticsearch, Logstash, Kibana, Suricata, Zeek (previously known as Bro), Wazuh, and many more.
It can be utilized in a wide range of ways, such as;
- NIDS- It aggregates network events from Zeek, Suricata, and other technologies to provide comprehensive network coverage for your firm.
- HIDS- It works with host-based event collecting agents such as Wazuh, Beats, and Osquery.
- Static Analysis (PCAP Import)- It can import PCAP files to do rapid static analysis and case studies.
10- Suricata

Initially designed as an Intrusion Detection and Prevention (IDS/IPS) tool, it has now evolved to include key protocol detection and Network Security Monitoring (NSM) functions.
Some of its outstanding traits are as follows:
- Suricata can log HTTP request logs and save TLS certificates, as well as extract and store files from flows.
- IDS/IPS
- Automatic Protocol Detection for HTTP on any port and application of the appropriate detection.
11- Graylog
It’s worth a look because of its scalability, user-friendliness, and functionality.
Graylog’s outstanding qualities include:
- Dashboards that let you select which measures or data sets to track and evaluate.
- Built-in fault tolerance allows for multi-threaded searches to analyze multiple potential threads at the same time.
Zen Networks is a leading provider of advanced IT solutions, specializing in log monitoring, automation and DevOps.
Our expert team offers a wide range of services, including IT monitoring, cloud services, agile solutions, and automation. We are also well-versed in the installation and implementation of Elasticsearch, Logstask, and Kibana on Docker.
By leveraging our extensive domain expertise and innovative technologies, we empower our clients to optimize their IT infrastructure and achieve operational excellence. Our solutions are designed to help organizations of all sizes to streamline their processes, improve efficiency, and reduce costs.
We invite you to take advantage of our complimentary consultation and quote service to learn more about how we can help your organization to achieve its IT goals. Contact us now to schedule your consultation and discover the benefits of working with Zen Networks.
Error: Contact form not found.
Author